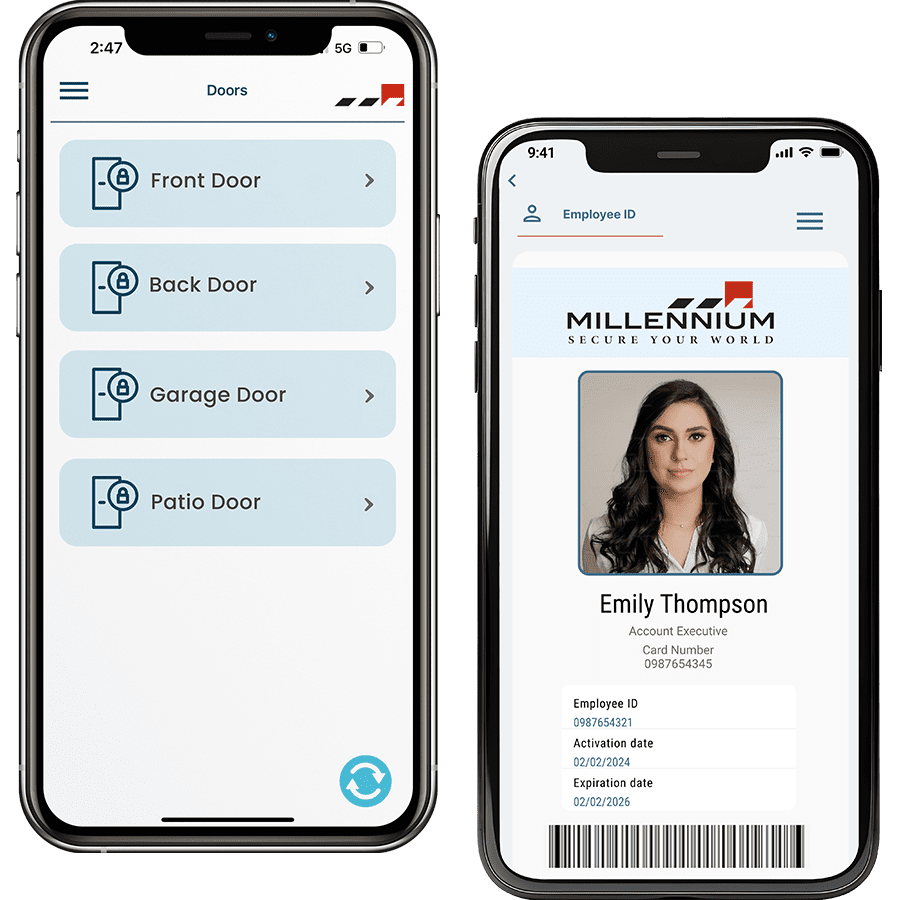
A mobile access control system enables smartphones, tablets, and smartwatches to serve as digital keys, providing convenient, secure access to restricted areas. This technology is rapidly transforming the access control industry, offering a more efficient and flexible solution compared to traditional keycards, fobs, and badges. With the rise of IoT and smartphones, mobile access control is becoming a preferred choice for organizations worldwide, as illustrated by a Gartner report stating that 20% of organizations have transitioned from physical to mobile credentials
What is a Mobile Access Control System?
Mobile access control replaces physical access methods with digital credentials stored on mobile devices, allowing secure access through Bluetooth Low Energy (BLE), Near Field Communication (NFC), and cloud-based remote access. By integrating these technologies, the system allows proximity-based access through secure connections between the reader and the mobile device.
For additional convenience, many systems also allow remote access. This feature enables users to unlock doors from any location via a mobile app, ideal for granting access to remote employees, temporary workers, or visitors without requiring physical presence at the site. The accessibility and flexibility of this feature significantly expands use cases for mobile access control, particularly in larger buildings and geographically dispersed facilities.
How Does a Mobile Access Control System Work?
A mobile access control system has five core components similar to traditional access systems: access points, personal credentials, readers, control panels, and access servers. However, instead of relying on physical cards, mobile access control uses digital credentials stored on smartphones. By integrating BLE and NFC technology, the system allows proximity-based access through secure connections between the reader and the mobile device.
Mobile access systems can also leverage cloud-based remote access, allowing administrators to grant or revoke access from anywhere, making it a convenient solution for managing multi-site operations or providing temporary access.
The Advantages of Mobile Credentials
Superior Security Measures
Mobile credentials are more secure than traditional keycards and fobs. Key security benefits include:
- Unclonable Devices: Unlike physical cards, smartphones cannot be cloned, drastically reducing the risk of unauthorized access.
- Built-in Security Features: Mobile devices offer built-in security, including passcodes, fingerprint scanning, and facial recognition, adding multiple layers of protection.
- Two-Factor Authentication: High-security areas can implement two-factor authentication by requiring users to unlock their phones with biometric identification before access.
- End-to-End Encryption: Mobile access control systems offer encrypted communication between devices and access points, ensuring secure data transmission.
Enhanced Convenience for Users and Administrators
Mobile credentials streamline access management by eliminating the need to carry physical access cards. Users can rely on their smartphones for entry, which are less likely to be forgotten or misplaced compared to traditional credentials. Here are key convenience benefits:
- Hands-Free Access: BLE-enabled mobile access control systems allow users to gain entry simply by approaching the reader, removing the need for manual interaction.
- Motion-Activated Entry: Some mobile readers offer motion-activated “Wave to Unlock” features, enabling touchless access.
- Remote Unlocking: Through cloud connectivity, authorized users or administrators can remotely grant or revoke access, making mobile credentials an ideal solution for multi-site management.
Cost-Effectiveness and Operational Efficiency (Enhanced Content)
A mobile access control system reduces the long-term costs associated with traditional physical access control. Key cost-saving features include:
- No Physical Credential Expenses: Mobile credentials eliminate the need for purchasing and managing physical cards, fobs, or badges, leading to lower overhead costs.
- Cloud-Based Management: Mobile access systems often use cloud storage for credential management, eliminating the need for on-premises servers and reducing maintenance expenses.
- Minimal Hardware Investment: Since most employees already have smartphones, organizations can skip the cost of issuing dedicated hardware, making mobile access highly cost-effective.
Types of Mobile Access Control System Technology
Mobile access control utilizes several key technologies to enable secure and convenient access. Here’s an overview of each technology and its applications:
1. Bluetooth Low Energy (BLE)
BLE technology enables devices to communicate over relatively long distances, allowing users to access buildings hands-free. BLE-based systems typically connect to readers without manual pairing, making access seamless and user-friendly.
2. Near Field Communication (NFC)
NFC enables close-range communication between the reader and the mobile device, requiring a tap on the reader to gain entry. This method is especially popular in high-security applications where controlled, intentional access is a priority.
3. Cloud-Based Remote Access (New Content)
Many advanced mobile access systems now support remote unlocking through cloud-based connections, allowing users or administrators to grant access from anywhere. This feature has become increasingly relevant in today’s hybrid and distributed work environments, where remote management is essential for security and convenience.
Mobile Access Control System: A Safer and Smarter Solution
Research suggests that around 74% of Americans feel uneasy without their phone. This statistic highlights a key advantage of mobile access control—users are unlikely to forget or lose their mobile credentials, as they are always with them. This level of reliability means that security teams are more likely to be notified if a phone is lost or stolen, enabling rapid deactivation of mobile credentials to prevent unauthorized access.
In comparison, 17% of physical credential users lose at least one keycard or fob every year. These lost credentials can lead to significant security risks, including potential breaches and unauthorized access. By upgrading to a mobile access control system, organizations can ensure that lost or stolen credentials are immediately revoked, minimizing the vulnerability that comes with physical keys or fobs.
Why Mobile Access Control is the Future of Security
The shift towards mobile access control aligns with broader trends in workplace security and digital transformation. Organizations are increasingly looking for flexible, future-proof access solutions that can adapt to changing operational needs. As cloud technology, IoT, and mobile device usage continue to evolve, mobile access control systems are uniquely positioned to offer enhanced security, convenience, and cost savings.
Mobile access control also integrates seamlessly with other security technologies, such as video surveillance and IoT-based security sensors. By consolidating multiple security functions within a single ecosystem, organizations can gain a more holistic view of their security landscape, supporting better incident management and faster response times.
Conclusion:
Mobile access control systems offer a secure, convenient, and cost-effective alternative to traditional physical access solutions. By leveraging BLE, NFC, and cloud-based remote access, organizations can benefit from enhanced security and streamlined access management. With features such as hands-free entry, motion-activated unlocking, and remote access, mobile credentials cater to the needs of today’s digital workforce.
When selecting a mobile access control system, prioritize security certifications, essential features, and scalability to ensure a future-proof investment. As organizations continue to adopt mobile access technology, the industry is set to see ongoing innovation, further transforming how we manage and secure physical spaces.
Ready to Make the Switch?
Mobile access control offers unmatched security, convenience, and flexibility. Whether you’re looking to enhance the security of a single building or manage access across multiple locations, our mobile access solutions are designed to grow with your business. Contact us today to learn more about how mobile credentials can transform your access control system.
Millennium is a scalable, hosted, access control platform that services any type of real estate. Our cloud-based access solution allows managers and tenants to efficiently manage their physical security from anywhere while enhancing experience and driving profitability.