Unlock Maximum Access Control Potential With Integrated Video Surveillance
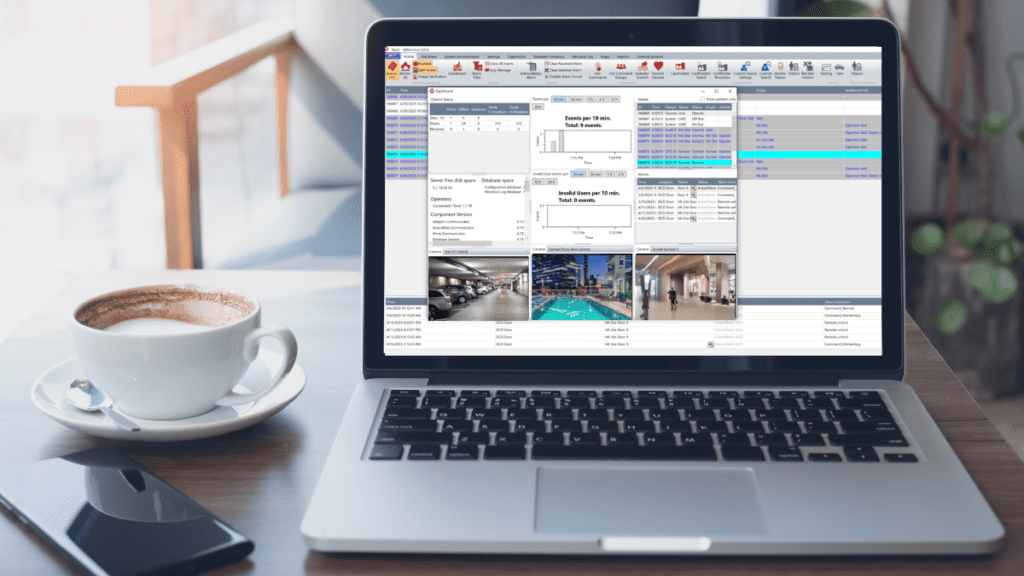
In today’s rapidly evolving world, ensuring the security and safety of our premises has become a paramount concern. Traditional security measures alone may not be enough to address the growing complexities of modern threats. That’s where the integration of video surveillance and access control systems comes into play. By combining these two powerful technologies, organizations can achieve heightened security, improved operational efficiency, and greater peace of mind. In this blog, we will delve into the reasons why integrated video surveillance with access control is not only good but also vital for comprehensive security solutions. Enhanced Situational Awareness: The integration of video surveillance and access control empowers organizations with a holistic view of their premises. By correlating access events with real-time video footage, security personnel can quickly respond to incidents, identify potential risks, and make informed decisions. This enhanced situational awareness enables proactive measures and timely interventions, significantly enhancing overall security levels. Accurate Identity Verification: Access control systems provide a valuable layer of security by restricting entry to authorized personnel. However, the integration with video surveillance adds an extra dimension of identity verification. By capturing video footage of individuals at access points, organizations can verify the authenticity of credentials and prevent unauthorized entry attempts. This powerful combination helps mitigate security breaches and strengthens access control effectiveness. Forensic Investigation and Evidence: In the unfortunate event of security incidents or breaches, the integration of video surveillance and access control plays a crucial role in forensic investigations. By correlating access events with recorded video footage, investigators gain valuable evidence for identifying culprits, understanding the sequence of events, and strengthening legal proceedings. This seamless integration simplifies the retrieval and analysis of relevant footage, saving time and resources during investigations. Operational Efficiency and Streamlined Processes: Beyond security benefits, the integration of video surveillance and access control systems brings notable operational advantages. Integrated systems allow for centralized management, eliminating the need for separate platforms and reducing complexity. Administrators can conveniently configure access permissions, monitor live video feeds, and generate comprehensive reports, all from a unified interface. This streamlined approach simplifies administrative tasks, enhances efficiency, and optimizes resource allocation. Scalability and Future-Proofing: The integration of video surveillance and access control systems offers scalability and future-proofing capabilities. As organizations grow or security requirements evolve, integrated systems can easily accommodate expansions and upgrades. With a flexible and scalable infrastructure, businesses can adapt to changing needs without significant disruptions or costly replacements. This future-proof approach ensures long-term investment value and prepares organizations for future security challenges. Cost-Effective Solution: When it comes to CCTV pricing, our integrated video surveillance and access control system offers exceptional value. Unlike traditional setups that require additional hardware and complex installations, our solution is cloud-based, eliminating the need for extensive infrastructure. With our system, all you need is a camera to capture footage, and everything else is seamlessly managed in the cloud with our Ultra App. This not only simplifies the setup process but also reduces costs, making it an affordable and convenient choice for organizations of all sizes. The integration of video surveillance and access control systems is a game-changer in modern security solutions. It provides a comprehensive and proactive approach to safeguarding premises, assets, and personnel. By combining real-time access control data with video intelligence, organizations gain unparalleled situational awareness, accurate identity verification, and streamlined operations. Moreover, the integration offers valuable forensic capabilities, operational efficiency, and future scalability. Embracing this powerful integration is not only good but imperative for organizations seeking robust and effective security solutions. Get in touch with us today to seize the full potential of video surveillance integration, bolstering your security stance and safeguarding what truly matters.